Manipulating AES Traffic using a Chain of Proxies and Hardcoded Keys
Intercepting and Manipulating client-side AES encrypted traffic in mobile applications having hardcoded Key and IV

Search for a command to run...
Articles tagged with #android
Intercepting and Manipulating client-side AES encrypted traffic in mobile applications having hardcoded Key and IV

Introduction Task Hijacking is a vulnerability that affects the applications running on Android devices due to a misconfiguration in their AndroidManifest.xml with their Task Control features.This allows attackers/malware to takeover legitimate apps ...
Android app Pentests can become torturous when you don't have the right environment setup.This of course refers to the SSL-pinning that is implemented in the apps which prevent Security Researchers from intercepting the traffic. There are a lot of gr...

Everybody is familiar with what an XSS is so fast-forwarding it a bit, this is a write-up on how I managed to get an XSS in a PDF generator on an Android application that allowed me to read local files on the system. Background A little background on...
TL;DRWe exploited an information disclosure in the mobile app to get an RCE on an internal server which was leveraged to the prod environment. Let's call the organization " Redacted Inc.".Their in-scope apps and URL's are their Android apps, and two ...

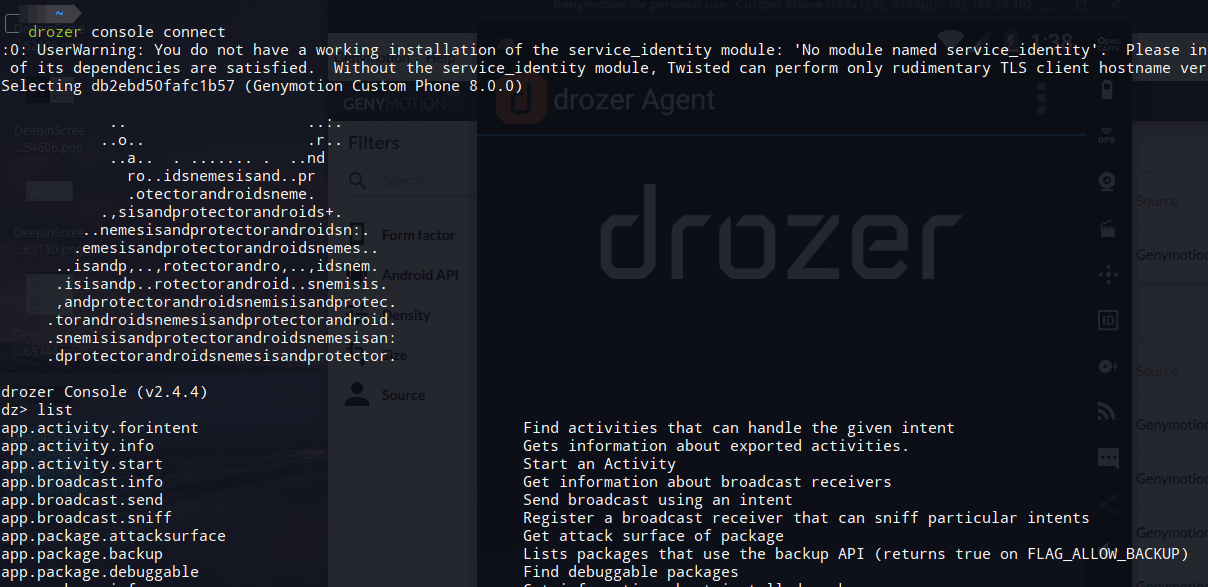
This post contains a list of commands which can be used with Drozer, a tool for pentesting Android applications.All of the commands have been taken from Mobile Application Hackers Handbook. It is one of the best Books out there to start with Android ...